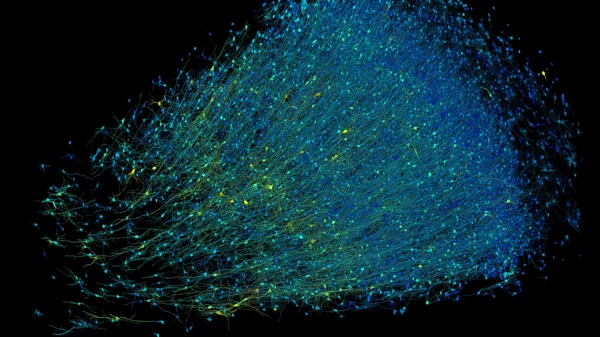
Researchers have uncovered a sprawling network of more than 70,000 legitimate websites that have fallen victim to a cybercriminal operation known as VexTrio.
Operating since at least 2017, VexTrio has largely operated under the radar, covertly manipulating website traffic to steer unsuspecting visitors towards malicious pages hosting malware, phishing scams, and other illicit content. Recent investigations have brought to light new insights into the inner workings of this shadowy network.
Operating much like marketing traffic distribution systems (TDSes), VexTrio employs a sophisticated setup to manipulate website traffic, utilizing tens of thousands of compromised websites to achieve its nefarious goals.
With around 60 affiliates involved, VexTrio functions as a profitable business model for its participants. Cybercriminals pay VexTrio to drive traffic to their malicious websites, while those responsible for providing compromised sites receive a share of the profits. Furthermore, the TDS also redirects users to scam sites directly operated by the VexTrio crew, maximizing their illicit gains.
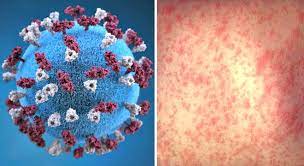
Flagged as a significant security threat by security firm Check Point, VexTrio’s extensive reach and complex infrastructure pose serious risks to online security. Another investigation conducted by Infoblox identified VexTrio as the most pervasive threat to its customers, with nearly half of the network’s domains detected within their networks.
One of the most notorious malware strains associated with VexTrio is SocGholish, also known as FakeUpdates, which emerged as the most prevalent malware in January. Targeting Windows systems, SocGholish is commonly distributed through compromised websites masquerading as legitimate browser updates. Once installed, it unleashes various malicious payloads, including backdoor malware and ransomware.
Additionally, ransomware attacks have surged in early 2024, with prominent groups like LockBit3, 8Base, and Akira leading the charge. However, it’s essential to approach these statistics cautiously, as they rely on data from ransomware groups’ leak sites, which may not always provide accurate or complete information.